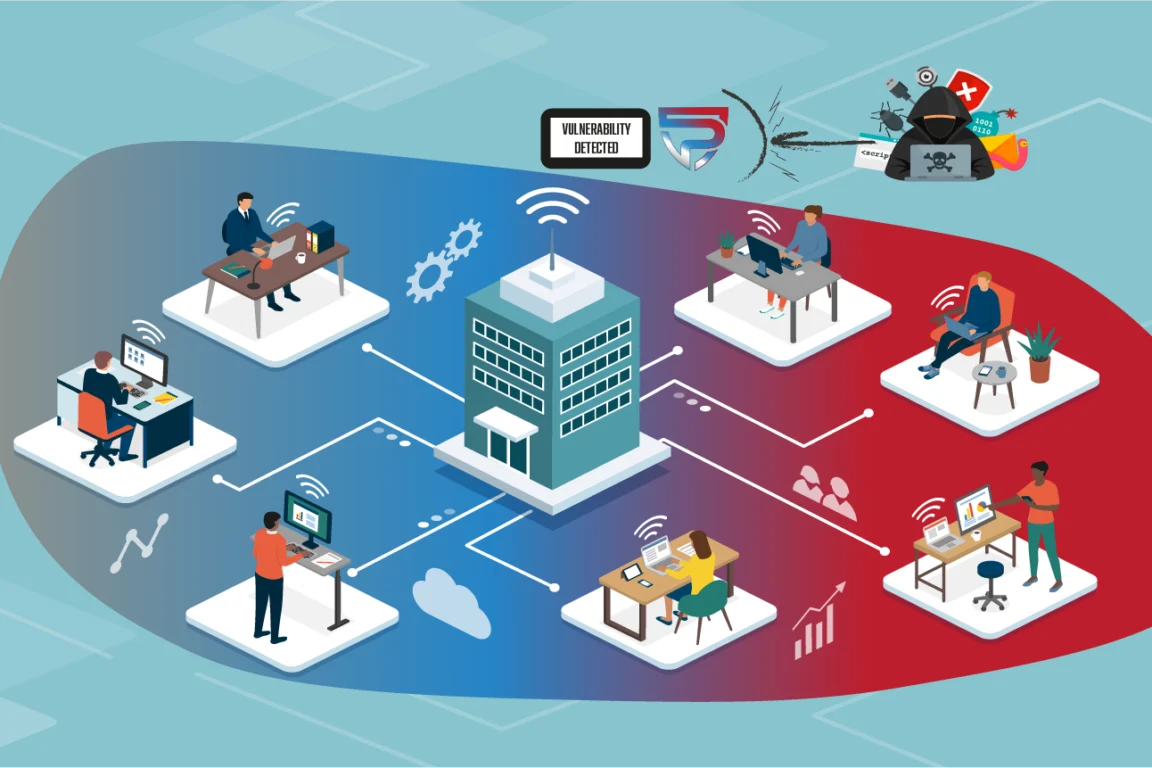
Critically assessing your system’s security, our penetration testing services simulate real-world cyberattacks to expose vulnerabilities while fortifying your defenses. By utilizing proven tools and custom techniques, we significantly reduce the attack surface. Moreover, our expertise spans various assets such as web apps, mobile apps, internal/external networks, medical devices, IoT devices, and other technical systems, ensuring comprehensive protection for your digital infrastructure.
What Are Penetration Testing Services?
Penetration Testing Services simulate real-world attacks on different components of your network, systems, applications, and products to identify security weaknesses. Also, integrate pen testing with your development operations processes to reduce costs, time, and vulnerabilities at each phase.
Pen testing can determine if you’re monitoring, analytics, and alerting catches malicious activities or indicators of compromise to identify blind spots in your threat detection. In contrast, web pen testing results can offer risk information needed to update WAF rules. Likewise, medical device manufacturers use pen testing to improve security, safety, and quality before FDA submission.
Praetorian Secure’s Pen Testing Approach
At Praetorian Secure we use a combination of testing methods to ensure a fully comprehensive/accurate testing program. These include: OSSTMM (Open Source Security Testing Methodology Manual), The Penetration Testing Execution Standard (PTES), Open Web Application Security Project (OWASP), The PTES Framework (Penetration Testing Methodologies and Standards), National Institute for Standards and Technology Cybersecurity Framework (NIST CSF) and more.
Our approach is to simulate a real-world attack and gain a snapshot of your vulnerabilities and security control weaknesses at a given point in time. Praetorian Secure continually researches the latest pen testing tactics and techniques to upgrade our testing capabilities. As we find new tools, we update or modify our test plans in our penetration testing collaboration suite.
Every pen test follows the same basic four steps to a certain degree they include information gathering/ discovery, analysis and exploitation, reporting and recommendations, and remediation with ongoing support.
Types Of Penetration Testing Services We Offer
 Application Pen Testing
Application Pen Testing
We will find vulnerabilities in your application code, app program interface(s) (APIs), web server configuration, database, and operating system (OS). To accomplish this we leverage the latest testing tools and methodologies. These include Open Web Application Security Project (OWASP), Open Source Security Testing Methodology Manual (OSSTMM), and Penetration Testing Execution Standard (PTES).
 Cloud Pen Testing
Cloud Pen Testing
Cloud Penetration Testing is like your standard pen test, where we check for vulnerabilities by simulating attacks but it is done in the cloud. In the realm of cloud security there is a shared responsibility between the Cloud Service Provider and client utilizing the service. When checking a 3rd party’s network you must always receive permission first, so check with you cloud provider before moving forward.
 Mobile App Pen Test
Mobile App Pen Test
We go beyond looking at API and web vulnerabilities to examine the risk within your mobile app environment. We have performed mobile pen testing on Android and Apple iOS for various clients. Our job is to target your mobile applications and gain access to sensitive data following the OWASP Mobile Application Security Verification Standard (MASVS) and other related methodologies.
 Medical Device Pen Test
Medical Device Pen Test
We safeguard healthcare integrity with our Medical Device Pen Testing Services. Our team will rigorously assess device security, identifying vulnerabilities, ensure the proper function of med devices, patient safety, check for compliance, and build consumer trust in your devices. The goal is to ensure innovation while safeguarding data and your reputation. Fortify your security solutions in a rapidly evolving cyber landscape.
 Network Pen Test
Network Pen Test
Our pen test experts use simulated attacks against your network scope to identify vulnerabilities and weaknesses in your defenses. We will use real-world methods that hackers would use to identify security problems in design, segmentation, security configurations, processes and security controls. These can be exposed from your internal and or external network(s).
 PCI Pen Test
PCI Pen Test
This type of pen test has a specific focus on PCI compliance requirements. We follow formal methodology approved by PCI Security Standards Council to confirm that all applicable PCI required controls are in place. At project kickoff we with your team to define scope, then complete the Rules of Engagement (ROE), and execute the test plan as it aligns with your PCI requirements.
 Social Engineering
Social Engineering
We provide phishing (email), vishing (voice), and smishing (SMS text) for organization’s looking to assess their security training and awareness practices. The best way to do this is provide a list of your employees and facilities you would like to assess and we will do the rest. After our tests are completed we will provide recommendations and give employees instant feedback when they make mistakes.
Meeting Your Pen Testing Goals
The first step in penetration testing should be defining the Rules of Engagement (ROE) agreement for approval. For example, some clients prefer the MITRE ATT&CK framework, allowing security teams to test their defenses quickly against known adversarial techniques. For the best return on investment, penetration testing activities should have a defined scope, timeframe, and objective that meets your company’s needs.
Moreover, professional penetration testing methodologies should be as efficient and comprehensive as possible based on the timeframe and funding allotted for testing. Typically, the ethical hacker performing the pen test will complete a threat modeling after the intelligence gathering phase to prioritize potential weaknesses for exploitation.
Finally, penetration testing reports should identify where exploitable vulnerabilities exist and provide detailed evidence and recommendations for vulnerability resolution. Additionally, the final report should be input into your internal risk management process. Based on the severity and impact (for example, CVSS Scoring), your internal risk management process should cover reviewing and adjudicating all findings. Afterward, develop a comprehensive remediation plan with prioritized timelines for fixed actions based on risk. Executives should be part of the cross-functional risk management process to gain insight and approve the plan and residual risk level.
Benefits Of Pen Testing
-
Reveal Current Vulnerabilities
Testing provides detailed information about current security threats. Furthermore, it categorizes the severity of the vulnerability based on criticality, ranking from high to low. This helps easily and accurately manage your security system by allocating resources accordingly.
-
Test Before You Implement
Performing a pen test on new technologies before it goes to production saves time, money, and it is easier to fix the vulnerabilities before the application goes live.
-
Avoid Fines
Penetration testing keeps your organization’s major activities updated and complies with the auditing system.
-
Meet Compliance Regulations
You may need to meet industry and legal compliance requirements by performing penetration testing as specified. Various compliance frameworks require all managers and system owners to conduct regular penetration tests and security reviews.
-
Customer Security & Protection
Protecting customers data should be a top priority of all organizations. A breach of any customer data is not good, to say the last. Pen Testing protects your organization’s data and reputation from malicious threats.
-
Detailed Reporting
This includes an executive summary and technical findings with a a step-by-step breakdown and documentation of the exploitation process.
Penetration Testing Methods
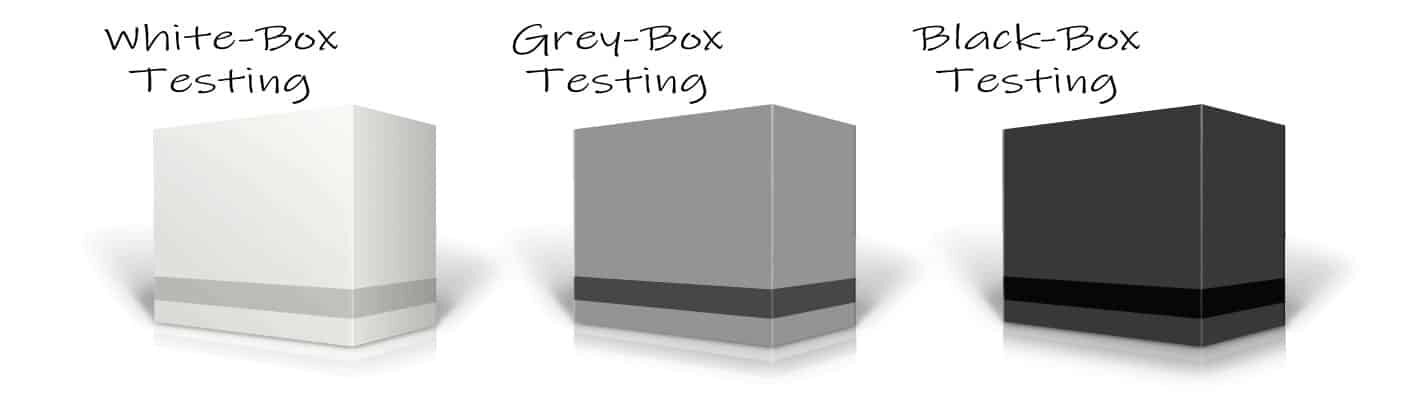
Over your companies lifespan, you have invested and implemented many security controls for the protection of your environment, data, and other technical resources. The question is, “will these past measures be enough far into the future?” If the answer is no, you may want to utilize our Penetration Testing Services to strengthen your current security posture. It does not matter if your looking for Internal or External, White-Box, Black-Box, or Grey-Box testing, manual vs. automated we can do it all. At the end of each penetration testing engagement we provide a report of the findings including action-based recommendations. The first step in finding a solution is to decide what kind of Penetration Testing Services you would be the best fit for your organization. Once you decide what is in-scope for the engagement it will be easy to determine the type of Penetration Testing Services that should be performed.
Post Testing Deliverables
Perform Penetration Test and provide the following:
- Executive Summary Report
- A document that summarizes the scope, approach, objectives, timeline, findings, and recommendations, at a high-level.
- Detailed Technical Report
- A document that outlines the granular vulnerability details (findings), attack vectors, and proof of concepts (repeatable results). Includes CVSS Severity Rating (low, medium, high, critical) for each finding.
- House Cleaning
- After our testing is completed we will remove all files, tools, and accounts used for testing and include details in our report.
- Fix Recommendations/ Action Plan
- Documents all your vulnerabilities and includes high-level fix actions.
Penetration Testing Steps
- Initial consult & demo
- Develop Rules of Engagement (ROE)
- Scope identification
- Define goals & objective
- Intelligence gathering
- Threat modeling
- Vulnerability analysis
- Exploitation of vulnerabilities
- Post-exploitation
- House cleaning
- Report delivery including evidence & fix recommendations
- Presentation of the final report
Resources
Documents
Blogs
Videos
Identify your vulnerabilities with a penetration test, don't wait until it's too late.
One of our qualified pen testers will meet with you to discuss your pen testing goals and requirements. After, we will provide a scoping questionnaire for you to fill out and return. Then, we can provide a quote to you in 48 hours or less. Thank you for contact us.